May 16th, 2026
New
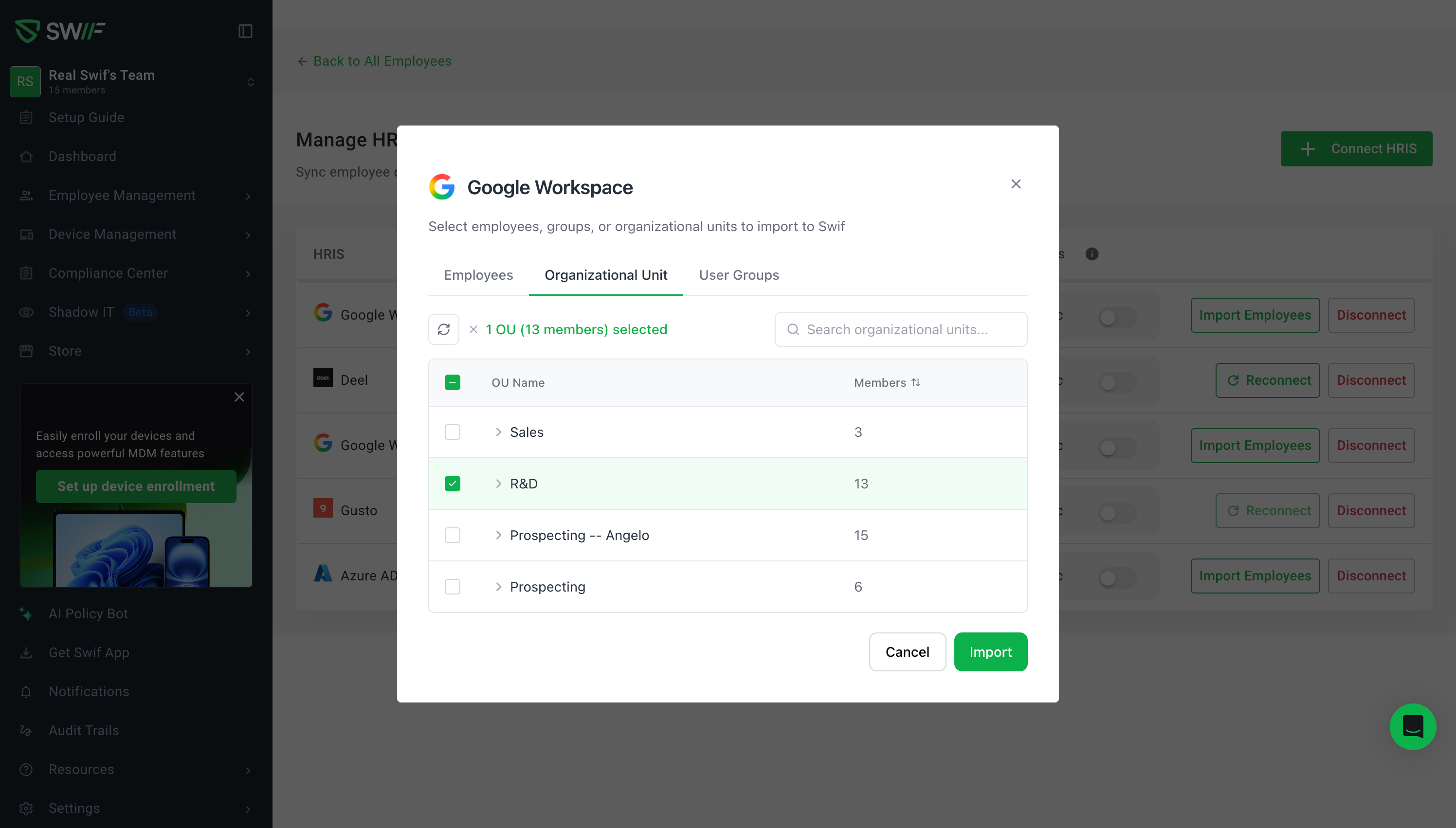
You can now import and auto-sync employees from Google Workspace using Organizational Units (OUs) — in addition to User Groups. This was one of our most-requested features.
What's new
Import by Organizational Unit — Select specific OUs during a Limited Import to bring in exactly the employees you need. OUs are displayed in a collapsible tree view, so you can drill into child OUs and pick the right scope.
Automatic User Group creation — Each imported OU automatically creates a corresponding user group in Swif, keeping your team structure in sync without manual setup.
User Groups tab — User Groups are now available as their own tab during import, separate from OUs, for clearer organization.
Redesigned Review Import step — The review screen before import now uses a tabbed layout (replacing the old accordion) with Will be imported and Will be skipped tabs, making it easier to verify what's coming in.
Updated Google Workspace Details Panel — After connecting, the details panel now includes dedicated Employees, Organizational Unit, and User Group tabs with proper empty states.
Reconnect flow for existing connections — Since this feature uses a new Google API scope, existing connections will show a Reconnect button to authorize the additional permission. New connections get it automatically.
Action menu cleanup — The Disconnect option has been moved into the action menu for a cleaner interface.
How to use it
Add Employees > Manage HRIS integrations (OU is a new scope so it needs a new GW connection)
Go to HRIS → Google Workspace and click Sync Google Workspace
Choose Limited Import and navigate to the Organizational Unit tab
Expand and select the OUs you want to import
Review the import summary and confirm
For full import, all employees (including all OUs) are synced automatically.
Note: If you already have a Google Workspace connection, you'll need to reconnect to grant the new Organizational Unit permission.
📖 Learn more in our help center
May 13th, 2026
New
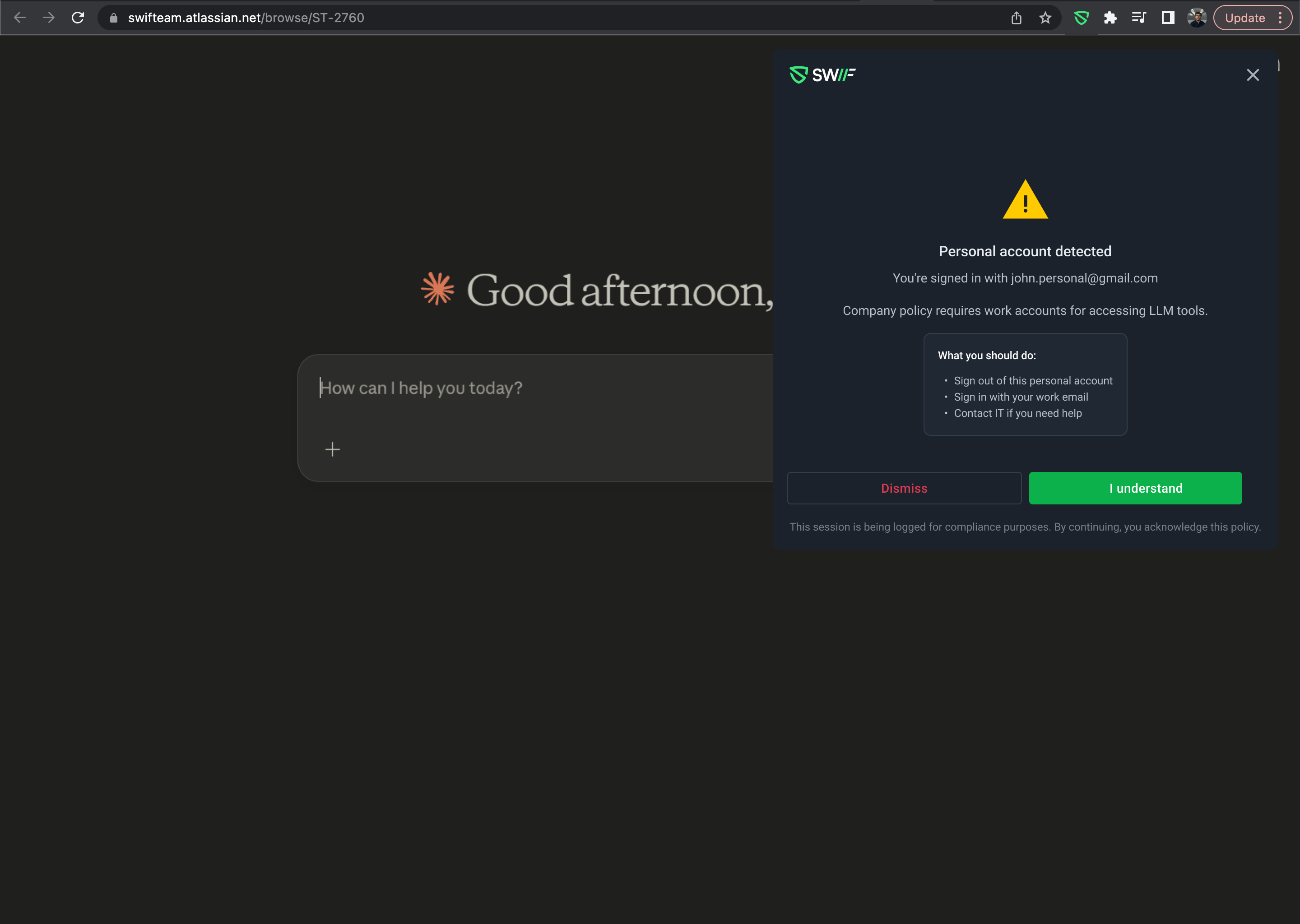
Monitor and control personal LLM usage across your team.
Admins can now create rules to detect and manage when team members use personal accounts on LLM tools like ChatGPT, Claude, Gemini, and more — helping keep company data within approved work accounts.
What's included
Create monitoring rules
Set work domains (your org domain is pre-filled automatically)
Choose which user groups to monitor
Select specific LLM tools to track (all selected by default)
Define what happens when a personal account is detected
Manage rules at a glance
View all rules in a filterable, sortable table
LLM tool badges with tooltip overflow when more than 2 are selected
Edit or delete any rule via the row action menu
Edit & delete rules
Edit dialog pre-fills current values for quick updates
Delete confirmation dialog prevents accidental removal
Success notifications confirm every action
Learn more → LLM Tracking: Monitor and Control Personal LLM Usage
May 12th, 2026
New
Released: May 7, 2026
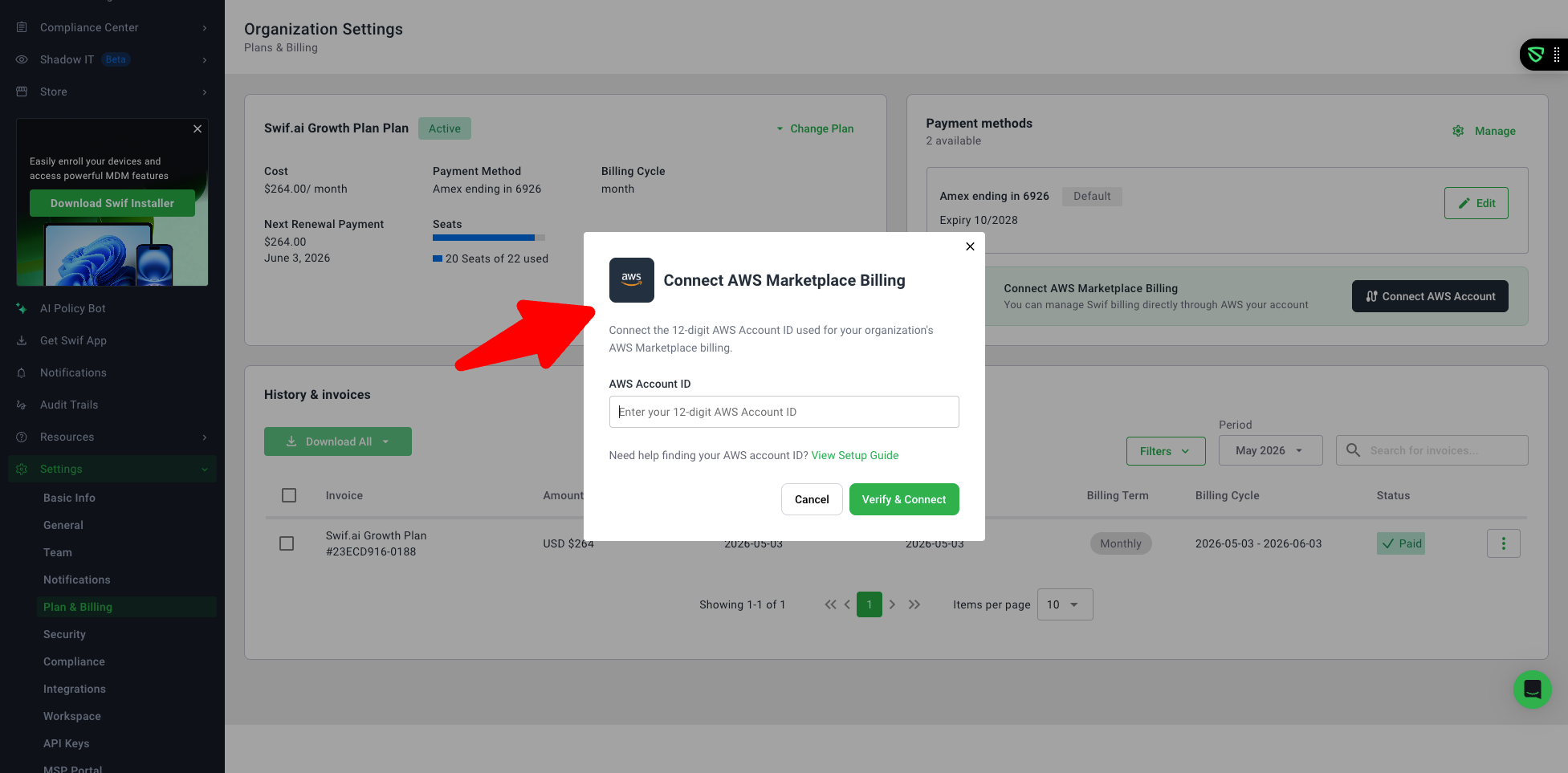
We've added full AWS Marketplace billing support to the Settings > Billing page, giving organizations the flexibility to manage their Swif subscription directly through AWS.
What's New
Connect & Manage Your AWS Account
Organization admins can now connect their AWS Marketplace billing by entering their 12-digit AWS Account ID directly from the Billing settings page.
Already connected? You can update your AWS Account ID at any time from the AWS Marketplace Subscription section.
AWS Subscription Details at a Glance
When an AWS Marketplace subscription is active, your plan details, subscription status, and billing information are displayed directly in the Billing page — no need to leave the app to check your plan.
A convenient "Manage in AWS Marketplace" link takes you straight to AWS for invoice and payment management.
Unified Billing Experience
Billing now clearly indicates your active subscription source — either Stripe (direct billing through Swif) or AWS Marketplace — so there's never any confusion about where your billing is managed.
Only one billing source is active at a time; the UI updates automatically when the source changes.
Additional Billing Improvements
New inline banner highlighting when billing is managed through AWS.
Updated subscription management dropdown with change and cancel options.
Refreshed Plan & Billing filters to reflect AWS subscription states.
Improved payment method management with a streamlined "Manage" flow.
Support users now see a clear message when they lack billing permissions.
Supported Plans
AWS Marketplace billing is available for Education, Standard, Growth, and Enterprise plans.
Learn More
For a step-by-step guide on connecting your AWS account, visit Managing Your Swif Subscription via AWS Marketplace.
May 6th, 2026
New
Released May 5, 2026
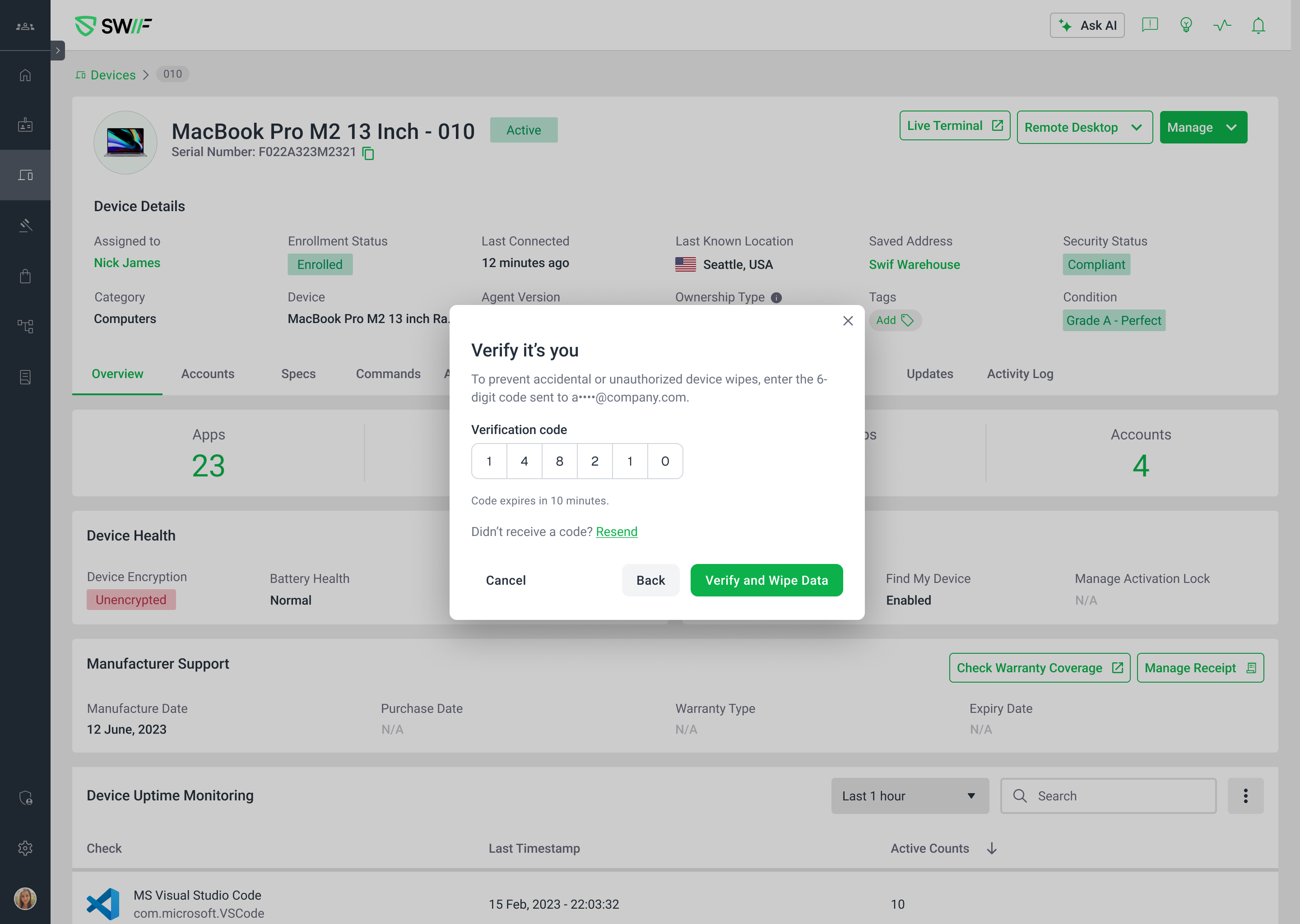
We've added an extra layer of protection for your most critical admin actions. Admin Safeguard requires identity verification via a one-time email code before any device wipe, soft wipe, or user removal can be executed — so these actions can never be triggered accidentally or by an unauthorized session.
What's new
Admin Safeguard toggle — A new setting under Settings → Security lets you require 2FA verification before destructive actions. It's enabled by default for all organizations.
Verified device wipe & soft wipe — When Admin Safeguard is on, the "Wipe Data" button is replaced with a "Continue" button that opens a verification modal. Admins must enter a one-time code sent to their email before the wipe executes.
Verified user removal — The same verification flow applies to removing a user account. The "Delete" button becomes "Continue", and deletion is blocked until a valid code is confirmed.
Resend code with confirmation — A "Resend code" option is available in the verification modal, with a toast notification confirming the new code was sent.
Error handling
Invalid or expired codes display clear inline errors — the destructive action is never executed.
Rate limiting kicks in after too many failed attempts to prevent brute-force attacks.
Closing the modal without completing verification cancels the action entirely. Re-initiating requires a fresh code.
Opting out
If your organization prefers the existing confirmation-only flow, you can toggle Admin Safeguard off in Settings → Security. All destructive actions will revert to their original behavior with no 2FA step.
Learn more
For a full walkthrough, see Admin Safeguard: Verification for Destructive Actions.
May 6th, 2026
Improved
Released: May 5, 2026
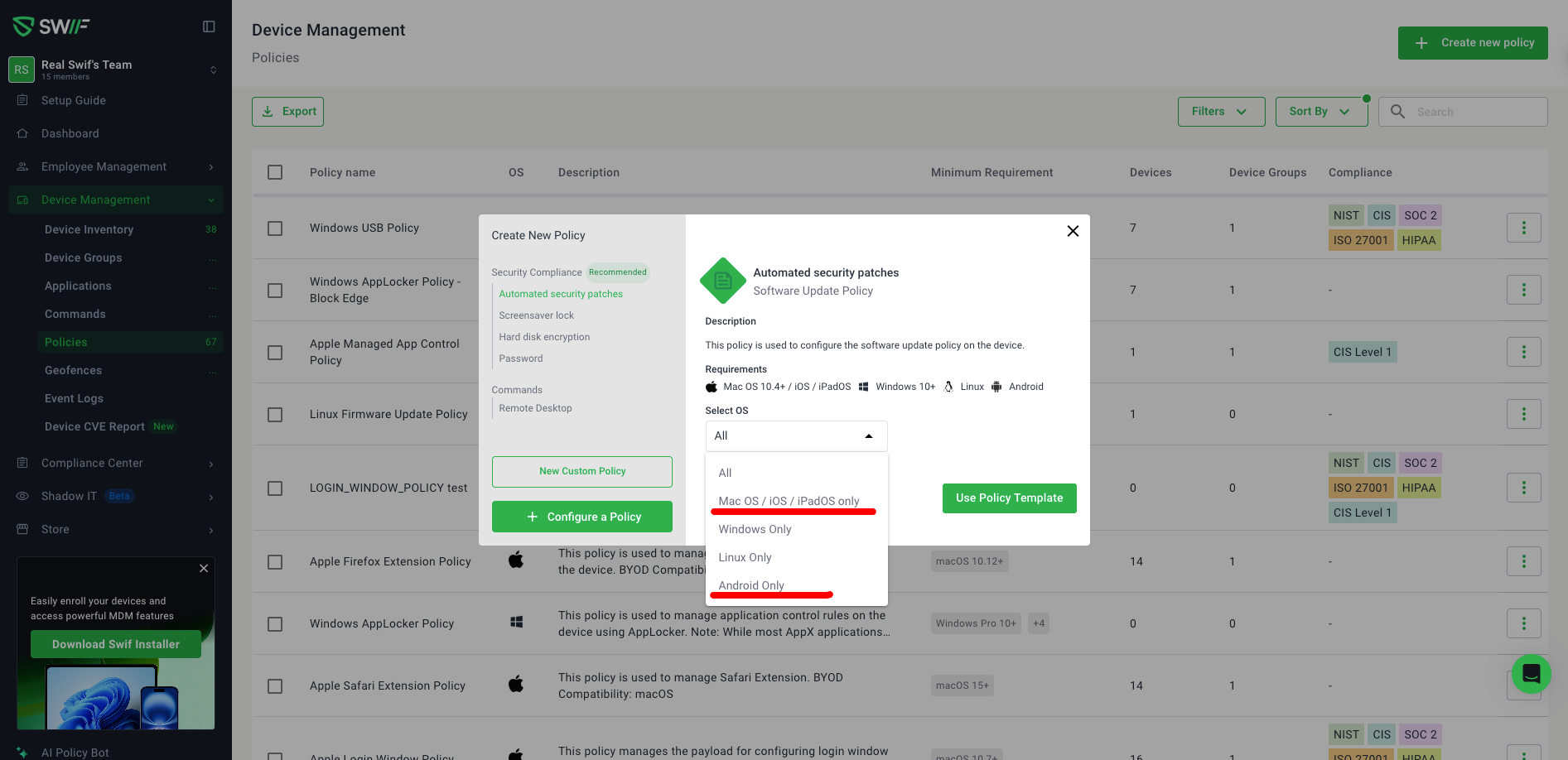
We've expanded our Security Compliance policy templates with full support for Android and iOS/iPadOS devices, giving admins more granular control over device policy configuration.
What's New
Android Policy Templates
You can now select "Android Only" as a target OS when creating Security Compliance policies. Four new Android-specific policies are available:
Android Software Update Policy — enforce software update requirements on Android devices
Android Security Policy — manage hard disk encryption and security settings
Android Lock Screen Policy — configure screensaver lock requirements
Android Password Policy — set password complexity and rotation rules
The "Android Only" option is available across all four Security Compliance categories: Automated security patches, Screensaver lock, Hard disk encryption, and Password.
iOS/iPadOS Policy Templates
iOS and iPadOS are now supported alongside macOS through a combined "Mac OS / iOS / iPadOS only" OS selection option. Two policies cover these platforms:
Software Update Policy — enforce automated security patches across Apple devices
Password Policy — manage password requirements for macOS, iOS, and iPadOS
Note: macOS, iOS, and iPadOS share unified policies, so they are combined under a single selection option.
What Changed
The "Select OS" dropdown in policy creation now includes "Android Only" for all Security Compliance categories.
For templates that support iOS/iPadOS (Automated security patches, Password), the former "Mac OS only" option has been updated to "Mac OS / iOS / iPadOS only".
Templates that don't support iOS/iPadOS (Screensaver lock, Hard disk encryption) retain the original "Mac OS only" label.
Selecting a specific OS now correctly filters the Basic Configurations screen to show only the relevant policies for that platform.
April 30th, 2026
New
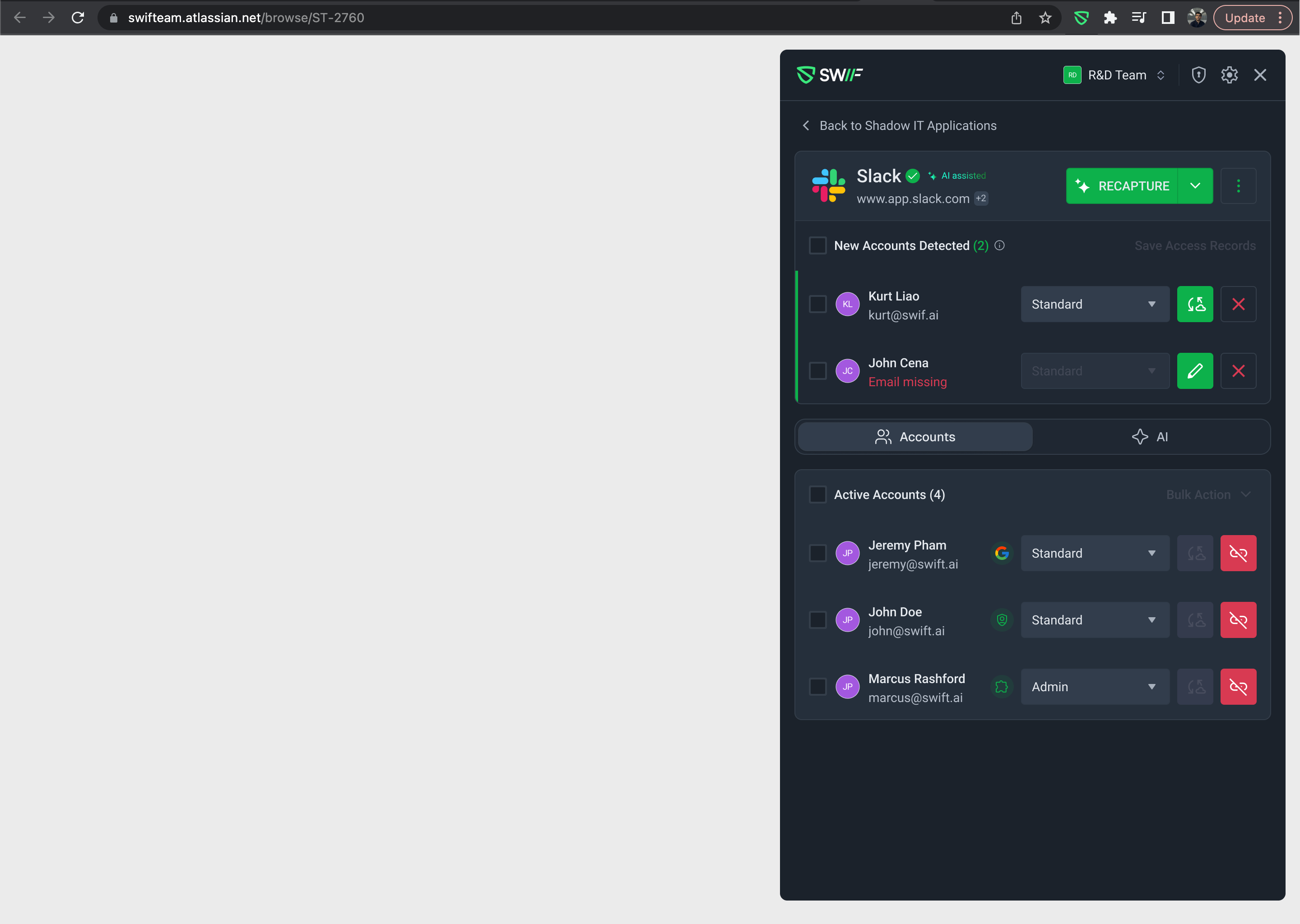
What Changed
Navigation reduced from 3 clicks to 0–1 — The browser extension now opens directly to the app page instead of requiring users to click through multiple menus.
New Behavior
Recognized domain — When you're on a website that maps to a known Shadow IT app, the extension opens directly to that app's Overview page with zero extra clicks.
Unrecognized domain — The extension opens to an All Applications view where selecting an app takes just 1 click.
Top-level tab navigation — The old "Back to menu" flow has been removed and replaced with persistent top-level tabs: "Shadow IT Apps" and "Employee".
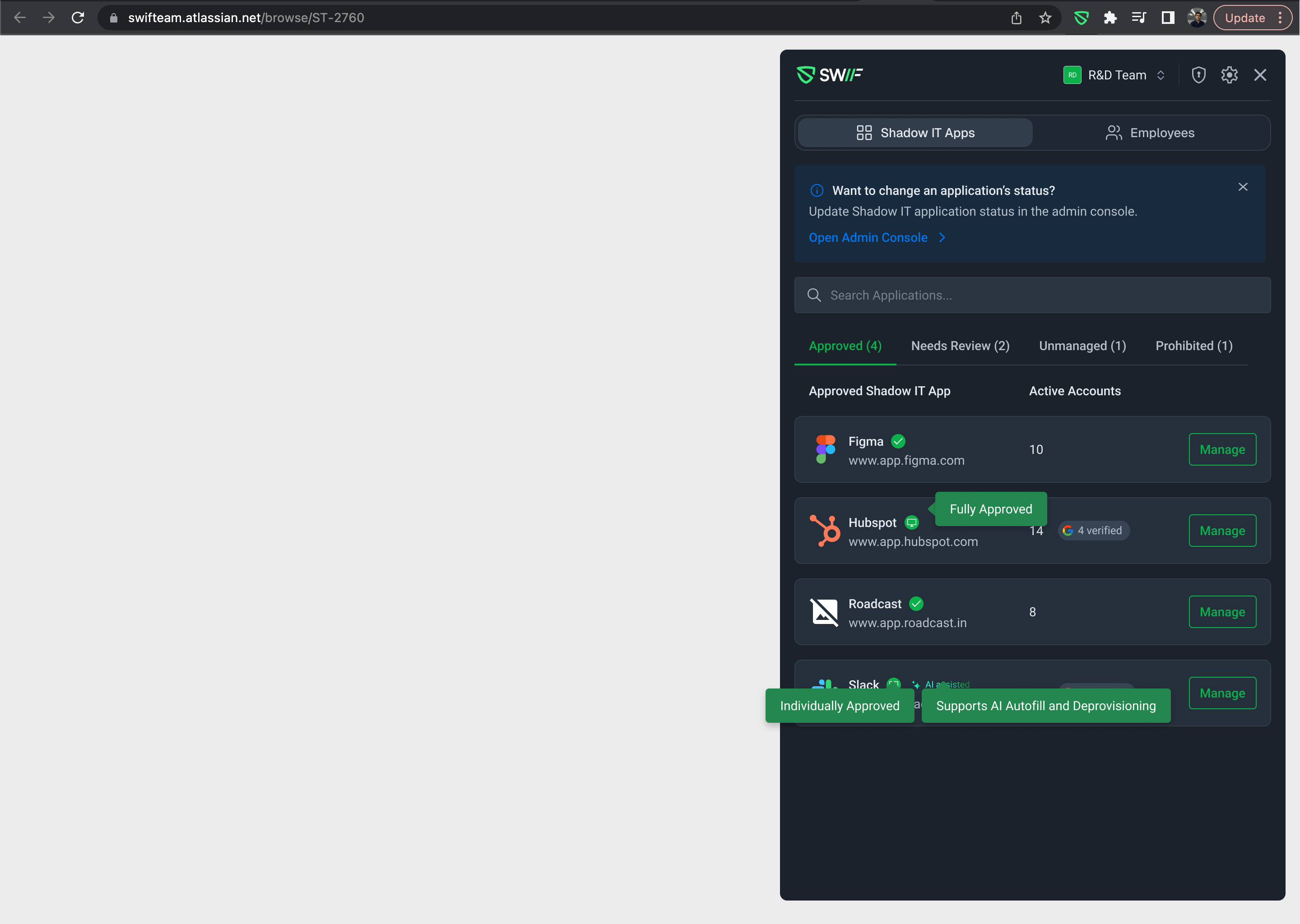
Search from main view — Users can search and switch between apps directly from the landing view without navigating through the old multi-step menu flow.
UI Updates
Overview as default landing page — The Shadow IT Apps Overview page is now the default view when admins open the extension.
Compacted navigation — The main page navigation has been streamlined for a cleaner, more focused experience.
Employee tab — Employee list is now accessible via a top-level tab alongside Shadow IT Apps.
April 29th, 2026
New
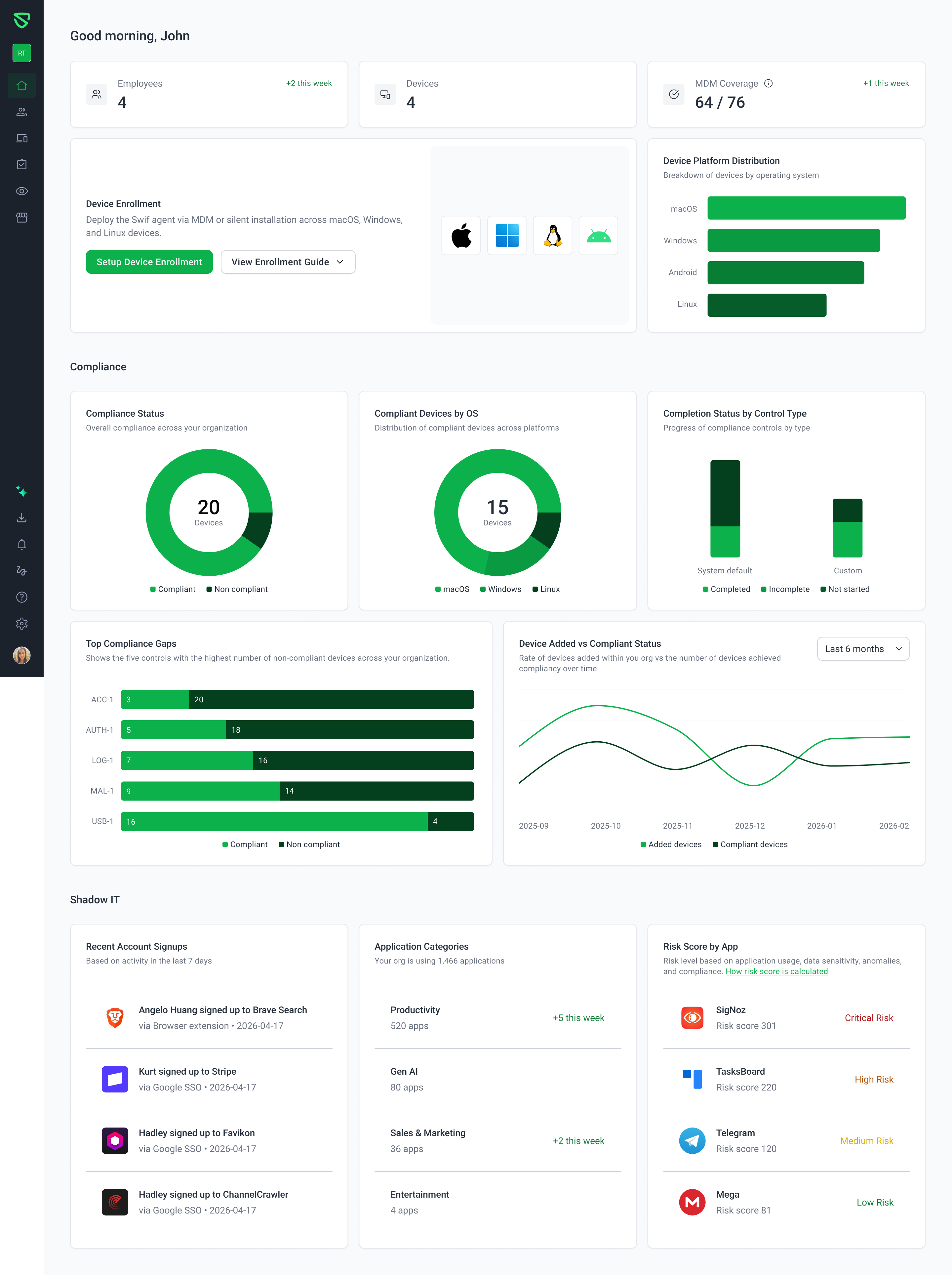
We've completely redesigned the main dashboard with a modern, consistent UI built on ShadCN components.
What's New
KPI Widgets — Employees, Devices, and MDM Coverage are now displayed as clean KPI cards with absolute weekly increments (e.g., +5 this week) instead of percentage trends, making changes easier to understand at a glance.
Device Platform Distribution — Replaced the old pie chart with a mixed bar chart for clearer platform comparisons.
Risk Score by App — Now shows a multi-app item-based list with risk scores and descriptions, replacing the single-app gauge chart.
Recent Account Signups — Switched from a table layout to a feed-style component for easier scanning.
Application Categories — Renamed from "All Applications," now includes a description and weekly growth indicators per category.
Chart & Info Tooltips — All charts and info icons now use standardized ShadCN tooltips for a consistent hover experience.
Dropdowns — Enrollment Guides and the Device Added vs. Compliant Status time range selector now use ShadCN Select components.
Removed
Compliance Controls Achieved widget — removed as it was always zero when fully compliant.
Shadow IT Needs Review widget — now covered in the dedicated Shadow IT Insights dashboard.
Improvements
Loading states — Skeleton loaders per widget instead of blank screens while data loads.
Empty states — Friendly messaging for first-time users or when no data is available.
Responsive design — Optimized layouts for desktop, tablet, and mobile with no breakage.
Accessibility — Full keyboard navigation, visible focus states, WCAG AA contrast compliance, and non-color status indicators.
April 29th, 2026
New
We've added the ability to automatically provision a default device account on macOS devices enrolled through Apple's Automated Device Enrollment (ADE).
What's New
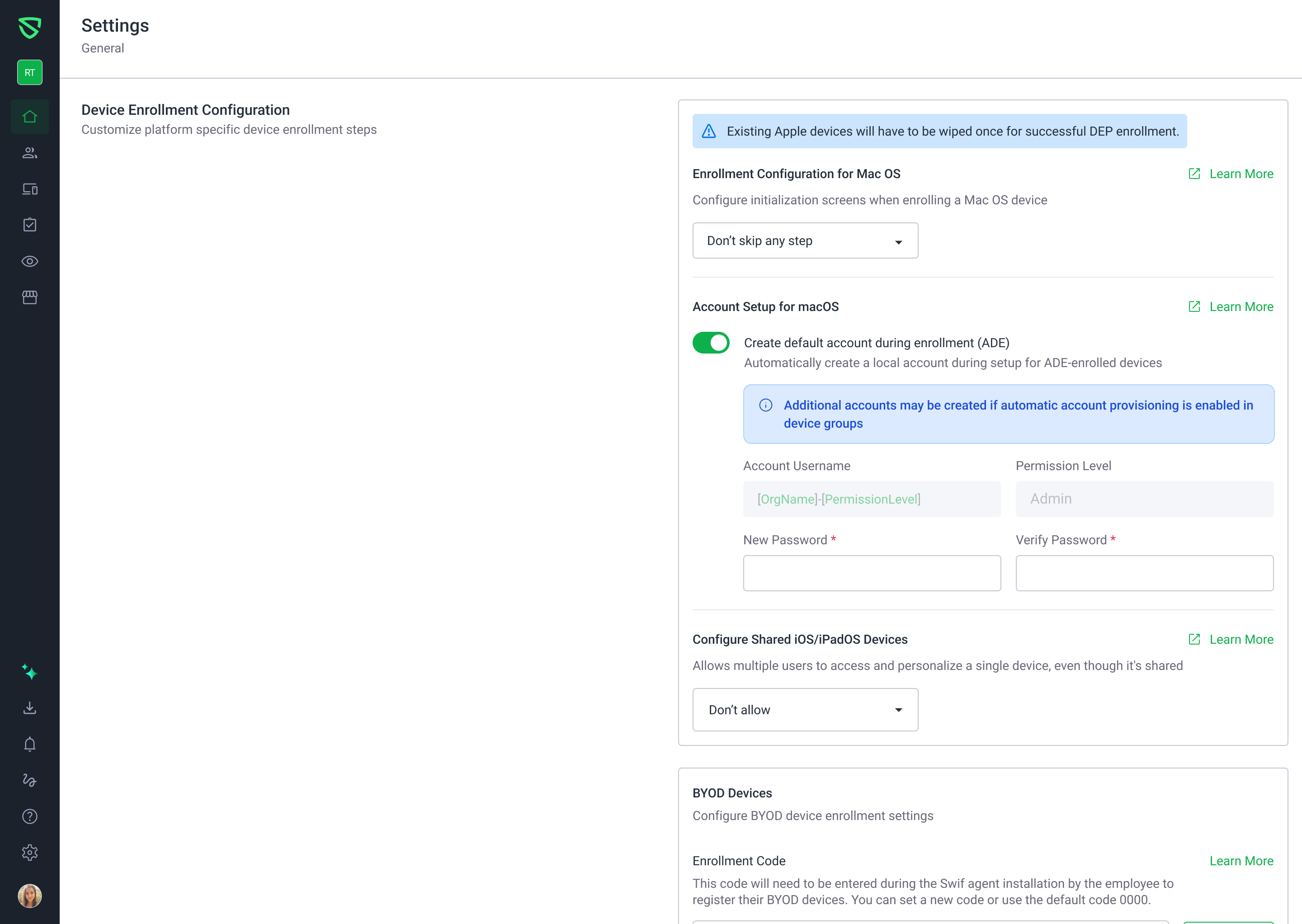
Account Setup in Device Enrollment Settings — A new "Account Setup for macOS" section is available under Settings > General > Device Enrollment Configuration. Admins can enable or disable automatic account provisioning with a simple toggle.
Default Account Configuration — When enabled, admins can set a default username and password that will be automatically applied to ADE-enrolled devices. The permission level is fixed to Admin (read-only).
Password Policy Detection — If an Apple password policy exists for the team, an informational alert is displayed below the password fields so admins are aware of the active requirements before saving.
Validation & Error Handling — The form validates for empty usernames, empty passwords, and password mismatches, with clear error messages and toast notifications.
Unsaved Changes Indicator — An "Unsaved changes" badge appears when inputs are modified, along with a Save Changes button to confirm updates.
How to Use
Navigate to Settings > General > Device Enrollment Configuration, enable the Account Provisioning toggle, fill in the desired username and password, and click Save Changes. Your team must have Apple Business Manager (ABM) linked for this feature to be available.
For more details, see the help article.
April 24th, 2026
New
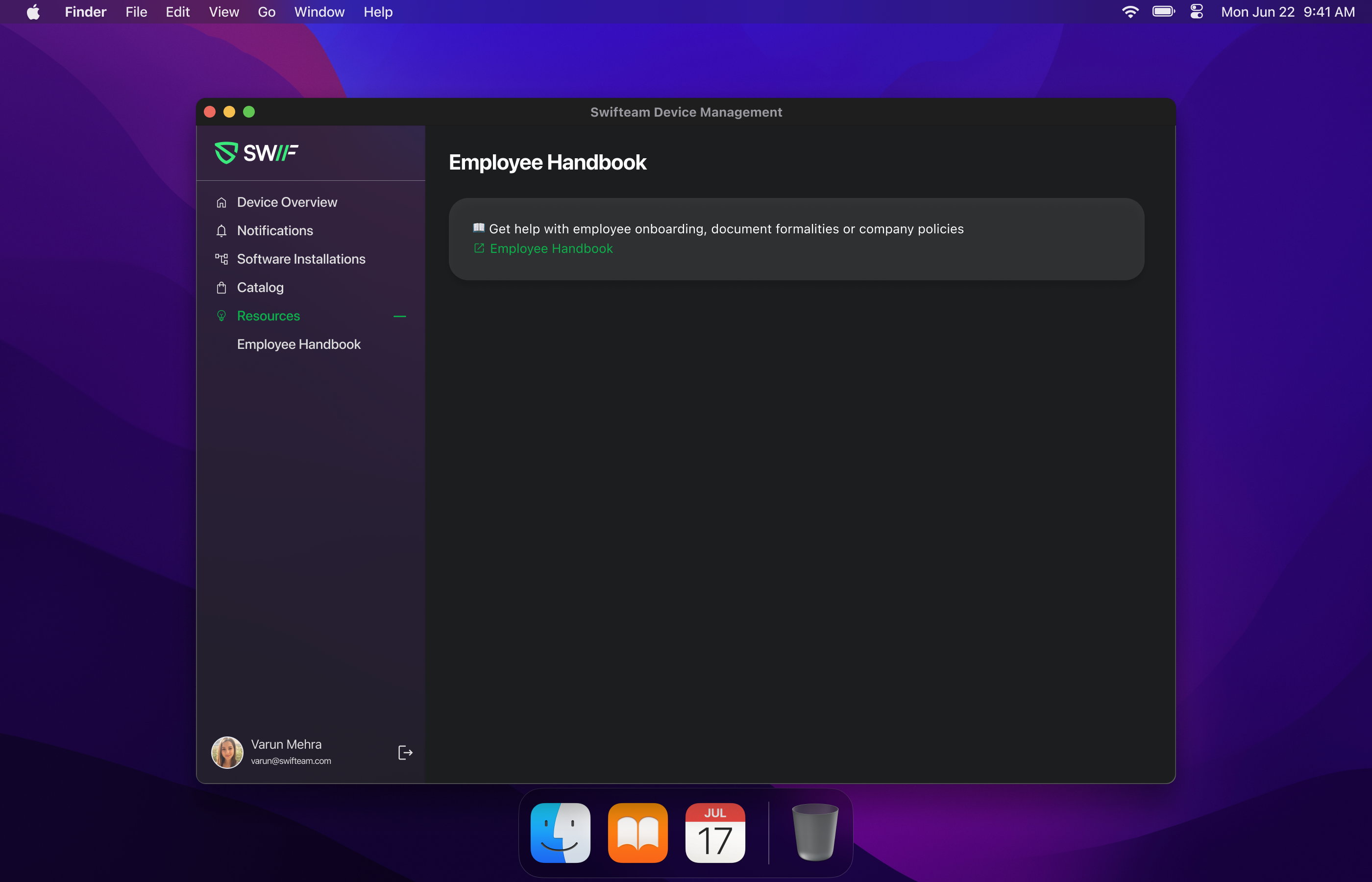
Admins can now add custom company resources — such as support portals, employee handbooks, internal wikis, and more — directly into the Swif desktop app.
What's new:
A new Learn / Resources section in the desktop app displays company-specific resource links configured by your admin under Workspace Settings.
When custom resources are configured, they replace the default Swif content (Newsletter, Blogs, Podcasts), giving employees a fully branded experience.
If no custom resources are configured, the default Swif resources continue to appear.
Availability: macOS, Windows, and Linux.
Learn more: Managing Swif's Desktop App UI and Company Resources
April 24th, 2026
New
Platforms: macOS, Windows, Linux (when allowed in policy)
Docs: Temporary Admin Elevation | Help Center | Swif.ai
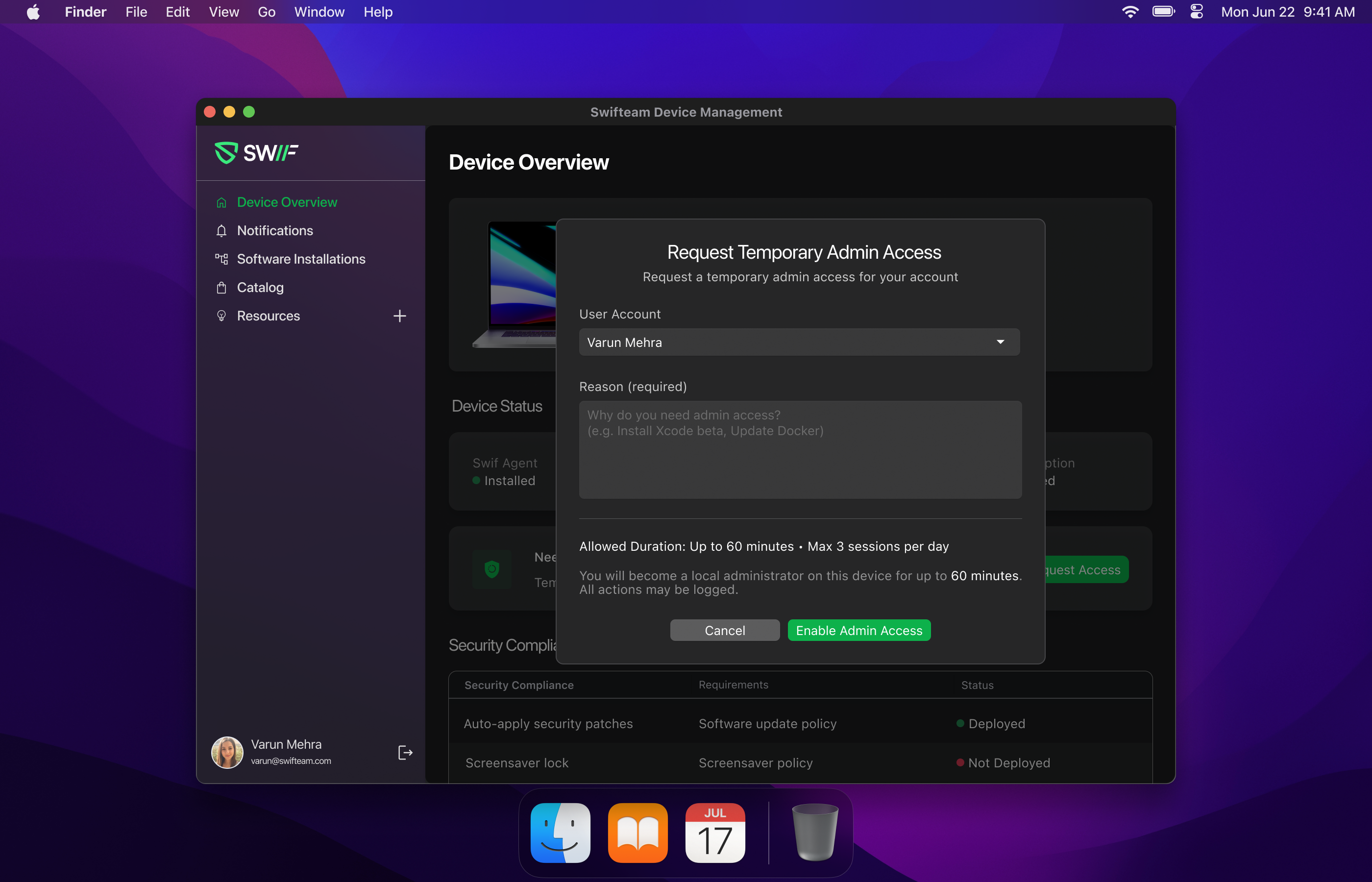
We’ve added a new end‑user flow in the Swif DeskApp that lets eligible users temporarily elevate themselves to local admin on their own device, based on the Temporary Admin Access policy configured in the Swif web app.
What’s new for end users
When Temporary Admin Access is enabled and the device/user is in scope:
New “Request temporary admin access” entry point in DeskApp
Appears on supported devices and OSes (macOS / Windows / Linux as allowed in policy).
Explains that admin access will be temporary and controlled by IT.
Request Admin Access modal
Users can:
See how long the admin session can last (per your policy).
Enter a reason for elevation (e.g., “Install Xcode”, “Update Docker CLI”).
The app validates required fields and shows clear inline errors if anything is missing.
On confirmation, the device enters elevated mode for the configured session duration.
Active elevated session view
When elevation is active, DeskApp clearly shows:
That the user is currently an elevated admin on that device.
A countdown timer for remaining admin time (auto‑updates during the session).
A primary action: End admin access now to drop back to a standard user at any time.
When the session ends (time‑out or ended early), local admin rights are automatically revoked and the UI returns to the non‑elevated state.
Guardrails & messaging
If elevation isn’t available (feature disabled, device out of scope, OS not supported, limits hit, cooldown active, etc.), DeskApp shows a clear explanation rather than offering the request option.
The backend enforces your configured rules (session duration, per‑day limits, cooldowns, etc.), and DeskApp surfaces friendly error messages when a limit is reached.
What’s new for admins
These changes work together with the existing Temporary Admin Elevation configuration and logs in the Swif web app:
Configuration lives in the web app
Configure under Settings → Local Account Controls → Temporary Admin Access:
Enable/disable Temporary Admin Access.
Scope to all devices or selected device groups.
Choose supported OSes (macOS / Windows / Linux).
Set max session duration, session frequency limits, and cooldowns.
Device‑level elevation history
Each elevation session from DeskApp is recorded and visible under:
Devices → [Device] → Device Details → Accounts → Temporary Admin Access log
For each session you can see:
Status (Active / Ended / Canceled / Failed).
Local account that was elevated.
Reason, start time, end time, and total duration.
Time remaining and an End admin access now control for active sessions.
For a full overview of configuration, user flows, guardrails, and logs, see:
Temporary Admin Elevation | Help Center | Swif.ai