September 29th, 2025
New
Device CVE Report – Key Features & Enhancements
The new Device CVE Report delivers advanced, actionable insights into device and software vulnerabilities across your organization. Here’s what’s included:
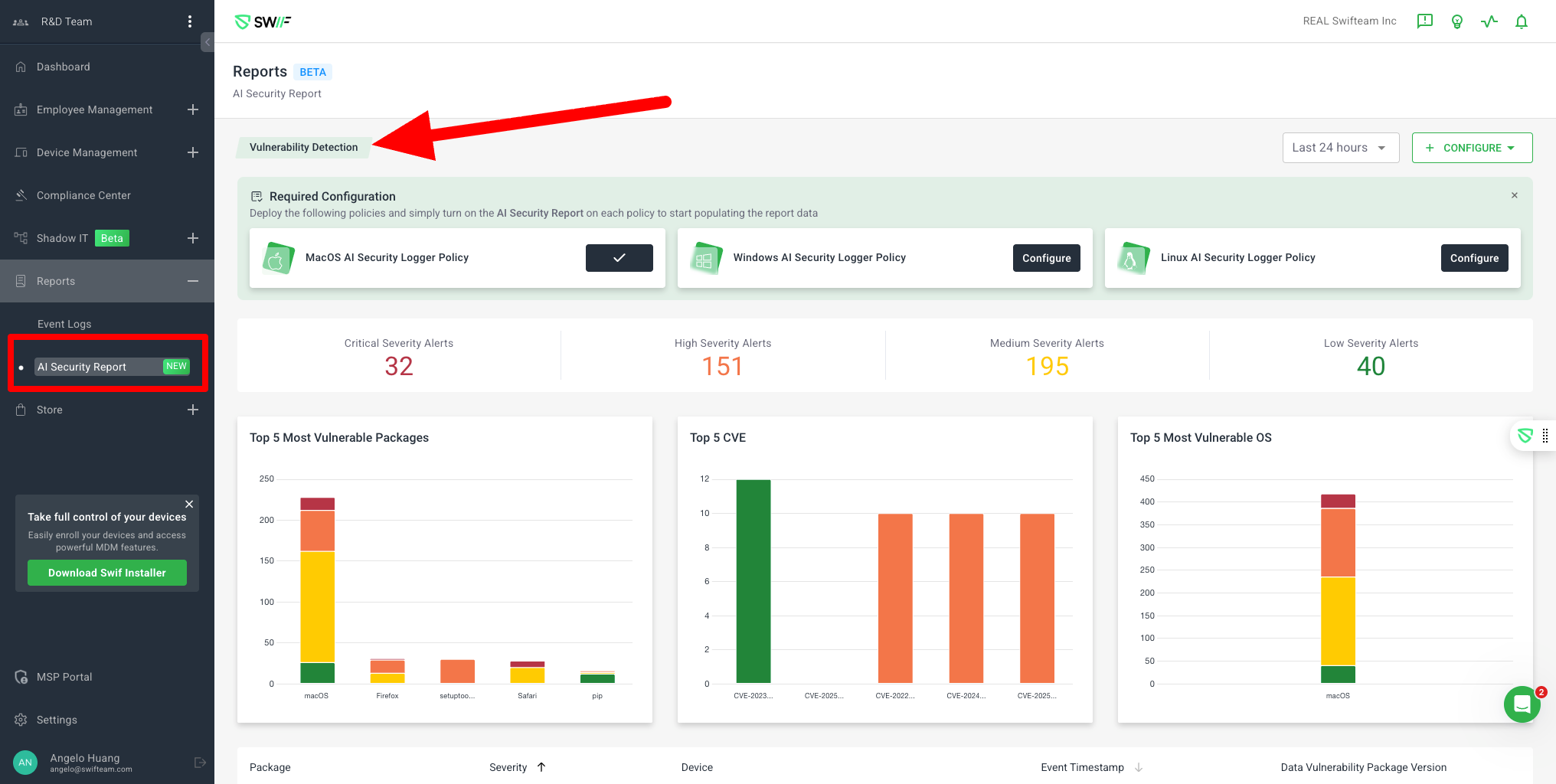
Centralized Dashboard & Navigation
Dedicated Device CVE Report Section: Easily accessible from the main navigation, highlighted as “NEW” under the Reports menu.
Policy Configuration & Onboarding
Required Configuration Guidance: Step-by-step instructions and visual cards for deploying Device CVE Report Policies on macOS, Windows, and Linux. Status indicators show which platforms are already configured and which need attention.
Vulnerability Detection & Visualization
Severity Alerts Summary: At-a-glance counts of Critical, High, Medium, and Low severity alerts, helping teams prioritize response.
Time Filtering: Filter vulnerability data by time range (e.g., “Last 24 hours”) for focused analysis.
Data Visualizations
Top 5 Most Vulnerable Packages: Stacked bar chart showing vulnerability counts by severity for the most affected software packages (e.g., macOS, Firefox, Safari, pip).
Top 5 Device CVEs: Bar chart highlighting the most frequently detected Common Vulnerabilities and Exposures (Device CVEs) across your environment.
Top 5 Most Vulnerable OS: Visual breakdown of vulnerabilities by operating system, with severity color-coding for quick risk assessment.
Detailed Alerts & Remediation
Severity Alerts Table: Searchable, sortable table listing all detected vulnerabilities, including device, package, version, description, severity, and Device CVE ID.
Expanded Alert Details: Click any alert for a detailed description, risk assessment, and clear, actionable mitigation steps (e.g., update OS, restrict network access, monitor activity).
Pagination & Filtering: Easily browse through large numbers of alerts with pagination and items-per-page controls.

User Experience & Support
User Profile Integration: See which devices and users are affected, with clear device identification.
Notifications & Support: In-app notifications and quick access to support or chat for immediate assistance.
Device Enrollment Prompt: Prominent call-to-action to enroll devices for full coverage.
This release empowers security and IT teams to quickly identify, prioritize, and remediate vulnerabilities, with intuitive visualizations and actionable guidance.
👉 For a full list of the latest improvements and key features, see our Device CVE Report article.