March 12th, 2026
New
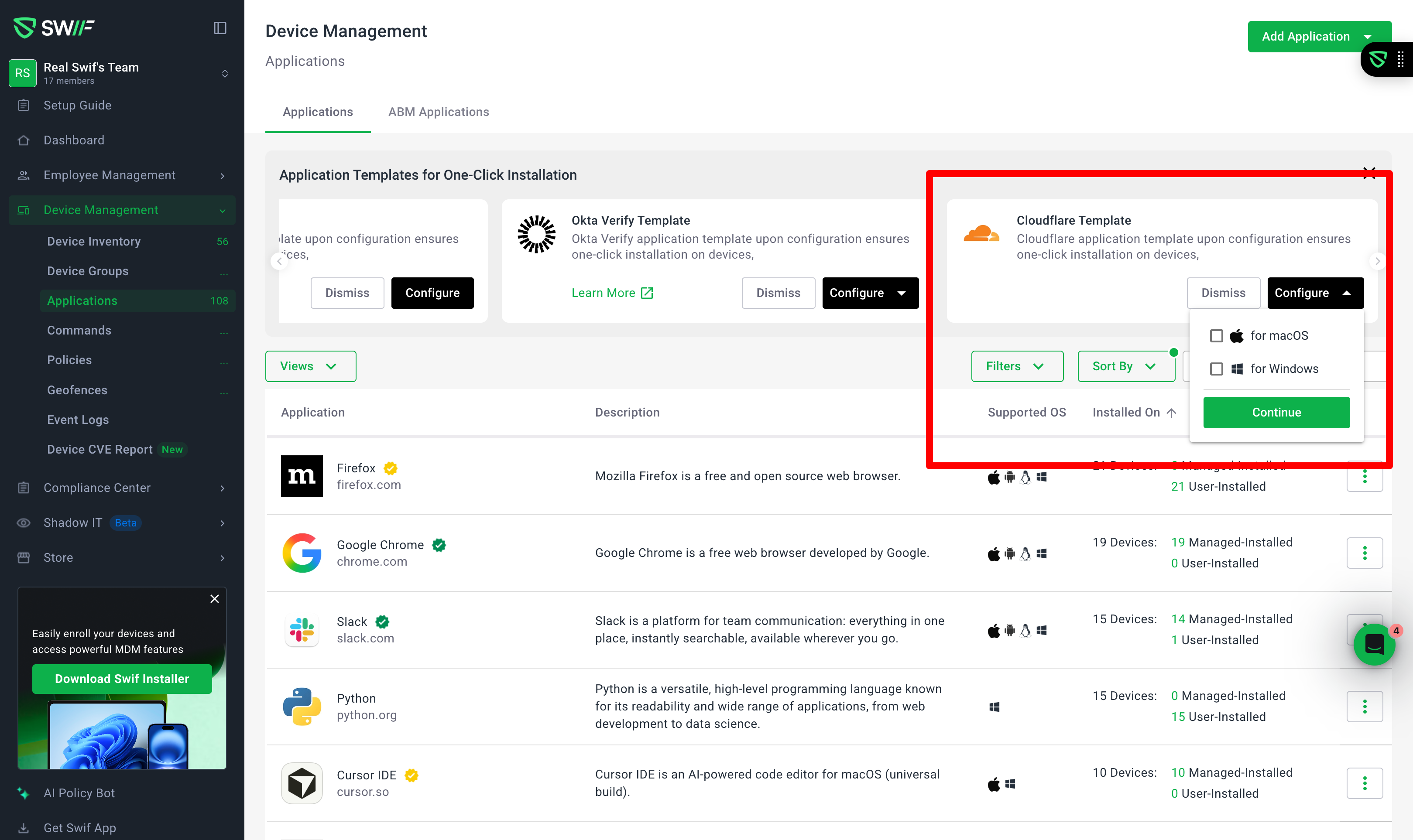
New: Cloudflare WARP app templates for macOS and Windows
We’ve added first‑class Cloudflare WARP app templates for both macOS and Windows to make it easier to deploy Cloudflare’s ZTNA/VPN client with the right certificates and configuration in place.
What’s new
Cloudflare (macOS) app template
Available under Device Management → Applications → Software → App Templates as a macOS‑only template.
Preconfigured with Cloudflare metadata (name, vendor, description, tags such as Network Security / VPN / Cloudflare).
Designed to work together with a Cloudflare certificate/profile policy so certificates are installed system‑wide before WARP runs.
When you instantiate the template as a custom app, Swif generates a mobileconfig profile for WARP, with clearly marked placeholder fields (e.g.
{"id":"6809779837658c5d4fd67537","name":"swifai","displayName":"Swif.ai","customDomain":"feedback.swif.ai"},,) that your team can replace with your own Cloudflare WARP configuration values.
Cloudflare (Windows) app template
Available in the same App Templates library, scoped to Windows only.
Preconfigured with Cloudflare app defaults and a Windows‑appropriate installer type (MSI/EXE).
Includes a post‑install script that creates the required Cloudflare WARP configuration file at:
C:\ProgramData\Cloudflare\mdm.xml
The script writes a ready‑to‑use XML structure for multiple WARP configurations (e.g. WireGuard/Masque endpoints), ensuring the config is in place immediately after installation.
Certificate handling and policies
macOS
The Cloudflare (macOS) template is designed to be used together with a certificate profile.
The template surfaces guidance that Cloudflare’s root/intermediate certificates must be deployed before app installation, and that admins should review and update the generated mobileconfig to match their own Cloudflare tenant and endpoints.
Windows
The Cloudflare (Windows) template is wired to use a
WINDOWS_CERTIFICATE_INSTALL_POLICYfor certificate deployment.The policy includes an
encodedCertificatefield (Base64) that is intended to be supplied by the customer. The template and related policy UI clearly indicate that this value must be replaced with the organization’s Cloudflare certificate.This keeps certificate material out of the template itself while still making the flow repeatable across customers.
Multi‑tenant / customer‑specific configuration
Both templates are parameterized so different organizations can use the same base templates:
Certificate bodies and WARP config values are not hard‑coded to a specific customer (e.g. Opus); instead, they are provided as editable fields/strings.
Admins can create multiple custom Cloudflare apps from the same templates, each with their own certificates and configuration values.
Admin experience and safety
Discoverable templates
“Cloudflare (macOS)” and “Cloudflare (Windows)” show up alongside other security/VPN templates (e.g. CrowdStrike, Okta Verify, Twingate) and behave consistently with them in filters and categories.
Clear pre‑install guidance
In the “Add Custom App → From template” flow, both templates surface a non‑dismissable notice reminding admins to:
Deploy Cloudflare certificates via the relevant certificate policy before rolling out the app.
Review and update the generated mobileconfig / policy content where placeholder values are present.
No regressions to other templates
Existing app templates and custom app flows continue to work as before; Cloudflare templates are additive and do not change installer options, categories, or performance for other apps.
Learn more at Deploying Cloudflare WARP via Swif: Mac and Windows App Templates with Certificate Handling.