May 6th, 2026
New
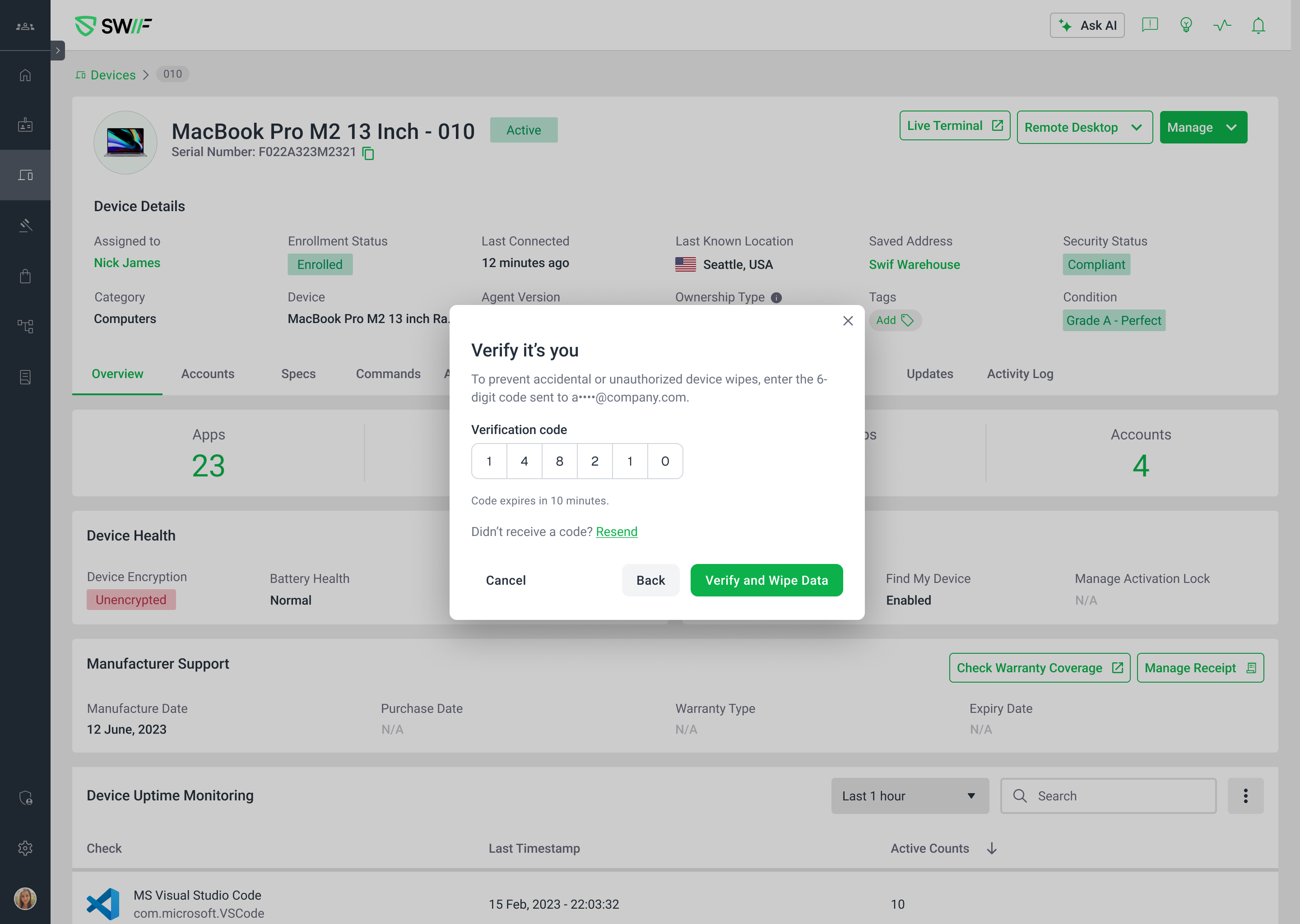
Admin Safeguard: Two-Factor Verification for Destructive Actions
Released May 5, 2026
We've added an extra layer of protection for your most critical admin actions. Admin Safeguard requires identity verification via a one-time email code before any device wipe, soft wipe, or user removal can be executed — so these actions can never be triggered accidentally or by an unauthorized session.
What's new
Admin Safeguard toggle — A new setting under Settings → Security lets you require 2FA verification before destructive actions. It's enabled by default for all organizations.
Verified device wipe & soft wipe — When Admin Safeguard is on, the "Wipe Data" button is replaced with a "Continue" button that opens a verification modal. Admins must enter a one-time code sent to their email before the wipe executes.
Verified user removal — The same verification flow applies to removing a user account. The "Delete" button becomes "Continue", and deletion is blocked until a valid code is confirmed.
Resend code with confirmation — A "Resend code" option is available in the verification modal, with a toast notification confirming the new code was sent.
Error handling
Invalid or expired codes display clear inline errors — the destructive action is never executed.
Rate limiting kicks in after too many failed attempts to prevent brute-force attacks.
Closing the modal without completing verification cancels the action entirely. Re-initiating requires a fresh code.
Opting out
If your organization prefers the existing confirmation-only flow, you can toggle Admin Safeguard off in Settings → Security. All destructive actions will revert to their original behavior with no 2FA step.
Learn more
For a full walkthrough, see Admin Safeguard: Verification for Destructive Actions.